How to Provide Access to Azure Resources with Azure AD
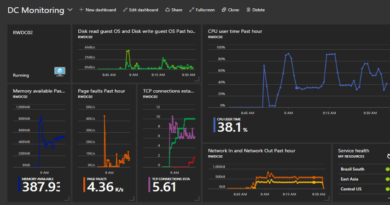
As part of the domain services activation, a virtual DC is automatically deployed in Azure. As such, deployment can take a bit. Be patient. The IP addresses of the provisioned DC is displayed once provisioned. Jot it down because it will be needed later when configuring DNS for the server network that will be deployed in the Resource Manager portal.
Configure Azure AD to Allow Domain Joins
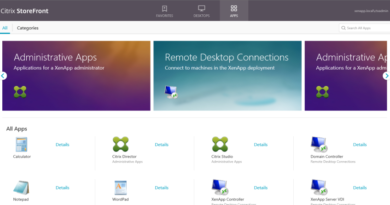
Before joining the virtual machines to the Azure Active Directory domain, switch over to the Classic Portal and provision a group, called AAD DC Administrators. The name must be exact. Once the group has been created, add your BWCAdmin@bluewidgetco.com account to the AAD DC Administrators group so it can be used to join machines to the domain. To reiterate – the group name MUST BE AAD DC Administrators.
Configure Server Virtual Network
With Azure Active Directory setup and synchronizing, go ahead and deploy a virtual network in the Resource Manager portal to house VMs in Azure. Create a vNet called ServerNetwork with an address space of 10.0.0.0/16 and a default subnet of 10.0.1.0/24. This will mean all of the VMs have an address of 10.0.1.x/24.
Configure Peering with Domain Services vNet
Before configuring DNS, you will have to configure peering so the server network can talk to the domain services network. Otherwise, your VM will not be able to see the BlueWidgetCoXXXX.com domain controllers. To configure peering, click on your ServerNetwork virtual network and click “Peerings” on the left side. From there you can add a peering with your DomainServices network. Leave all Configuration checkboxes unchecked.
Configure Server vNet DNS
With peering configured, connectivity between the two networks established. You can now configure DNS on the server network so go ahead and add the domain services DC IP address that you noted earlier as a custom DNS server for the 10.0.0.0/16 network.
Configure NSG for virtual network
To secure your server network and the eventual VM that you deploy to it, you will want to create a Network Security Group that locks down access. To do this, go into the Resource Manager portal, search the marketplace for “Network Security Group”, and deploy it to your existing resource group. Once the NSG is deployed, create an inbound security rule that only allows RDP from your workstation’s public IP address (visit ipchicken.com to check your IP).
Click here to join the Understanding Azure Facebook group or here for the latest Azure practice questions, answers, explanations, and reference materials.